
Generalities
A Virtual LAN, better known as a VLAN, is a LAN logically realized through the standard 802.1Q, which defines specifications that allow multiple virtual local area networks (VLANs) to be defined distinct, using and sharing the same physical infrastructure. The physical structure of a VLAN is not that of a normal local computer network but an abstraction that allows computers even located in places that are not physically close to each other to communicate as if they were on the same collision domain.
VLANs are nothing more than a layer of abstraction capable:
- to enable locations that are on physically distinct network segments to appear connected to the same logical network;
- to separate workstations that are on the same physical network and thus in the same broadcast domain into several distinct logical networks that are “disconnected” from each other.
Each VLAN behaves as if it were a local area network separate from the others where broadcast packets are confined within it, that is, communication at layer 2 is confined within the
VLAN and connectivity between different VLANs can only be realized at layer 3, through routing.
The main advantages of using VLANs are:
- savings: new VLANs are implemented on the same physical facilities as needed at the time, with significant savings in time and money;
- increased performance: the frame is not propagated to destinations that do not need to receive it due to the confinement of broadcast traffic to individual VLANs;
- increased security: a user can see only the traffic of its own VLAN and not of the others, even if they share the same connection hardware;
- flexibility: we have two situations in which the advantage is considerable:
– if the physical movement of a user is made within the premises reached by the infrastructure network, this can remain connected to the VLAN without changing the physical topology of the network but only with a simple reconfiguration of switches or bridges;
– if physical relocation of a computer is performed it still remains connected to the same VLAN without any reconfiguration of the hardware.
Implementation of a VLAN
Implementing VLANs requires that switches and bridges in the network infrastructure be capable of distinguish between different VLANs, and to do this they must observe the 802.1Q standard. The implementation of VLANs can be done in two ways:
- VLAN port based (untagged LAN or private VLAN);
- VLAN tagged (802.1Q).
In each case, VLANs must be defined within the bridge, with name and ID number to distinguish them from each other: first, each VLAN must be identified by a number, the VID (Virtual Identifier), which has range 1-1005 and its own address block.
In order to manage multiple virtual networks on the same physical structure, bridges must be able to perform three functions:
- ingress: the bridge must be able to figure out which VLAN an incoming frame belongs to from a port;
- forwarding: the bridge must know to which port the frame should be forwarded to destination based on which VLAN it belongs to;
- egress: the bridge must be able to forward the outgoing frame so that its membership in the VLAN is correctly interpreted by other downstream bridges.
VLAN detection by switches
One of the simplest applications realized by a VLAN is to “cut” a single physical switch into two or more different networks. For example, we could realize as in the figure two isolated networks using a single switch:
A- the red network is a VLAN with VID 20 and connects the 4 hosts (port 4,5,7,8);
B- the green network is a VLAN with VID 10 and connects the 4 hosts (port 1,2,3,6).
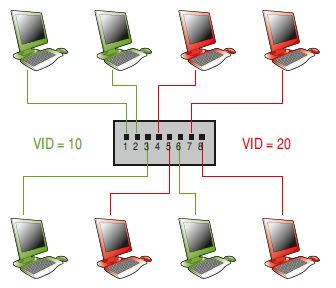
Green hosts will only see green hosts, and similar applies to red hosts: without VLANs it would be necessary to use two different switches, one for each VLAN.
Once a VLAN is defined, there are basically two techniques for associating hosts with it:
- using the switch’s port numbers: we might decide that the first half of the ports are reserved to the hosts in VLAN 20 and the remaining ones for those in VLAN 10; this is the simplest system but has major security limitations since the concentrator associates one of its ports with the VLAN and not to a host: whatever “device” is connected to the port becomes part of the VLAN;
- using addresses of the hosts’ network interfaces: if the VLAN is associated with the individual addresses of the hosts a more secure system is realized; in this case a host is connected to any port on the switch since it is recognized as belonging to the VLAN either by by its IP address, which we know, however, can be changed at any time, or its MAC address, which is unique and immutable for each interface.

Port based VLAN (untagged)
VLANs that use switch “port” numbers, that is, the static assignment of each port of the bridge to a VLAN, are called port based LANs. Ports can be assigned to different VLANs, and in this way a partitioning is achieved of the bridge into two or more logical bridges.

The operations to be performed by bridges are particularly simple:
- ingress: an incoming frame belongs to the VLAN to which the port is assigned, so no any other “membership recognition “mechanism on the frame;
- forwarding: the frame can be forwarded only to ports belonging to the same VLAN to which the the input port belongs to that is mapped to a forwarding database, separate for each VLAN;
- egress: once the port (or ports) through which the frame is to be transmitted has been determined, it can be transmitted as it is received, without being modified.
It is therefore not necessary for untagged VLANs to require compliance with the standard 802.1Q since all management is done within the switch, which must be properly configured (and configurable).
802.1Q VLAN (tagged VLAN)
The technology that allows two or more switches to share a VLAN by a change in the Ethernet frame format is one that uses the 802.1Q standard, which adds 4 bytes (TAGs) that carry information about the VLAN and additional ones. This technology is called tagged VLAN, also called VLAN trunking.
The first 2 bytes are called the Tag Protocol Identifier (TPI) and contain the EtherType tag (value 0x8100), a number that highlights the new frame format. The next 2 bytes are called Tag Control Information TCI (or VLAN Tag), structured as follows:
- user_priority: 3-bit field that can be used to indicate a priority level for the frame;
- CFI: 1-bit field indicating whether the MAC addresses in the frame are in canonical form;
- VID: 12-bit field indicating the ID of the VLANs; with 12 bits, 4096 VLANs can be defined: the first (VLAN 0) and the last (VLAN 4095) are reserved, so the actual usable IDs are 4094.
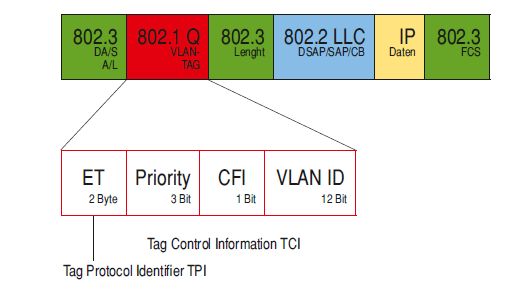
With these “additions,” it is possible for the frame to exceed a length of 1518 bytes, the upper limit of the Ethernet standard: bridges that admit 802.1Q standards must be able to accept frames with 2 extra bytes.
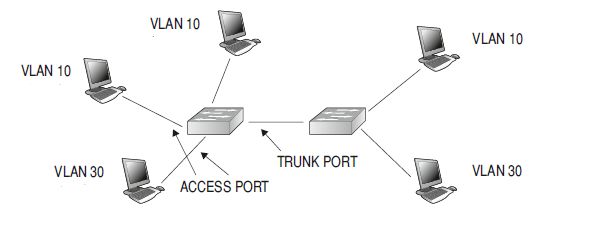
Packets with this format cannot arrive on any port of the switch since the switch must be able to interpret them: it is necessary to have a classification of the ports as well, which can be distinguished into trunk/tagged ports and untagged ports:
- if the port is associated with a “port based” VLAN (untagged) the frames received by that port do not need (and do not carry) TPI and TCI tags, nor will outgoing frames have to carry it; these ports are called access ports, and the link attested on those ports is called an access link;
- if the port is associated with one or more VLANs in tagged mode, the frames will carry the information of TAG and the VLAN to which the frame belongs is defined by the value entered in the TAG: these ports are called Trunk ports, and the link associated with such ports is called a trunk link.
Looking at the network depicted in the figure, we can definitely say that the ports that connect the two devices must be trunks since frames from multiple VLANs will be circulating in them.
Hybrid ports
The 802.1Q VLAN standard requires that a port must be able to be used in both modes i.e., it must be able to be associated with a VLAN in untagged mode or with other VLANs in tagged mode: in this case it is called a hybrid port. This port, as a first step, recognizes whether there are TGI and TCI tags in the frame: if these are not present, the frame is of the untagged type and therefore the port will operate in that mode; if, on the other hand, they are present, they are analyzed and the VLAN to which they belong is identified by the value of the VID.
The VLAN with which the port is associated in untagged mode is also called the PVID (Private Vlan ID).
The operations that bridges must perform in these cases are different from those described for untagged VLANs:
- ingress: first, the bridge must recognize the frame type and identify the VLAN to which it belongs and then:
– if the frame is untagged, the belonging VLAN is identified with the VLAN to which the port is associated in untagged mode;
– if the frame is tagged, the belonging VLAN is identified by TAGs; - forwarding: once the belonging VLAN is identified, the forwarding rules are applied and the output port is identified;
- egress: in this case it may be necessary to perform TAG insertion and removal:
– if the incoming frame is 802.1Q and the outgoing port is associated with the VLAN it belongs to in tagged mode, the frame is forwarded without modification;
– if the incoming frame is untagged and the outgoing port is associated with the belonging VLAN in untagged mode, the frame is forwarded without modification;
– if the input frame is 802.1Q and the output port is in untagged mode, it is necessary to remove the TPI and TCI before forwarding;
– if the incoming frame is of type 802.3 and the output port is associated with the VLAN it belongs to in tagged mode it is necessary to insert TPI and TCI before forwarding.
In the last two cases, the bridge must recalculate the CRC value of the frame before retransmitting it.
Of course, devices that do not support the 802.1Q protocol may coexist in a network: these will be connected on bridge ports associated exclusively with a VLAN in untagged mode so that each received frame will be associated with a VLAN and no 802.1Q frames will be forwarded to the downstream device, as TAGs are removed before the frame arrives.
In this way, there is no need to replace all the existing hardware in case you want to implement a VLAN: it is sufficient to insert only a few 802.1Q devices in an appropriate way and integrate them with the hardware existing, without having to replace it.
The network cards on the hosts must also be compatible, and generally they are not: the appropriate driver must also be installed, and finally, the operating system must provide the ability to use VLANs.
In the end
It is a good idea not to use VLANs to isolate different areas of the network, such as to host a DMZ, because traffic between VLANs is spoofable, i.e., easily forged: it is therefore always better to rely on a firewall to isolate the zones between which the security of the traffic is a critical factor.


